
Ben Grewell


Debunking the Myth: Unraveling the Truth About the Linux Kernel's Core Handling

Cracking Ansible Vault Secrets with Hashcat
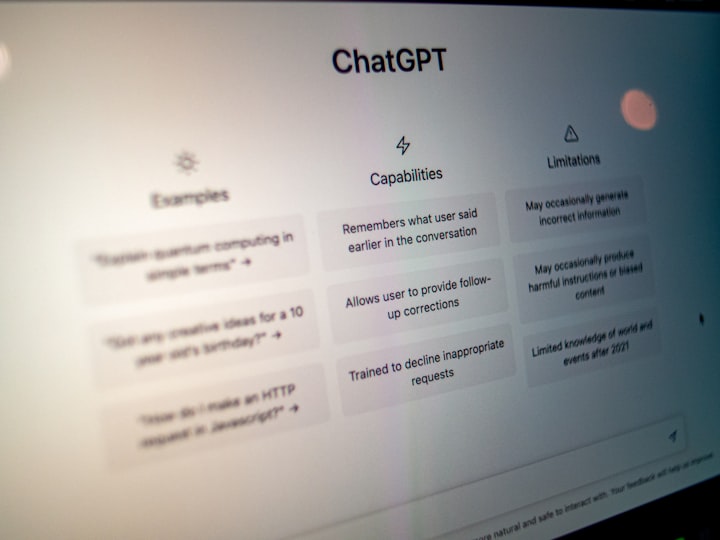
ChatGPT Unraveled: A Guide to Leveraging AI for Software Reverse Engineering

Leveraging LD_PRELOAD for Network Behavior Analysis: A Guide for Penetration Testers and Application Developers
