Inside Cybersecurity with Ben Grewell
Discover offensive security techniques, in-depth tech explorations, and programming guides to elevate your IT skills and keep you cyber-savvy in today's digital landscape.

Kubernetes RBAC Abuse: From system:anonymous to cluster-admin
A hands-on lab walking the full RBAC misconfiguration chain — unauthenticated API access to cluster-admin — with mitigations at each stage.

Why Your Kubernetes Pod Using macvlan Can't Talk to the Host
Understanding Host ↔ Pod Communication Issues with Macvlan in Kubernetes If you’ve implemented macvlan interfaces in a Kubernetes environment and you’re puzzled because your pod cannot communicate with the host—even though they’re on the same subnet—you are definitely not alone. This is a well-known behavior due

Debunking the Myth: Unraveling the Truth About the Linux Kernel's Core Handling
Introduction A recent article sparked discussions in the tech community by suggesting that the Linux kernel has been hardcoded to a maximum of 8 cores for nearly two decades. This claim prompts a closer examination to unveil the reality of core utilization in one of the world's most

Cracking Ansible Vault Secrets with Hashcat
Crack Ansible Vault secrets with hashcat. Step-by-step instructions and examples for extracting and converting vault entries, preparing for hashcat, and launching the cracking process. Unlock hidden secrets and enhance security assessment skills.

ChatGPT Unraveled: A Guide to Leveraging AI for Software Reverse Engineering
This week, we'll explore how ChatGPT can help with reverse engineering tasks. We'll be working with a program called "thingy," which is part of a computer security challenge. Since we can execute this software on a compromised host using sudo privileges, it's

Leveraging LD_PRELOAD for Network Behavior Analysis: A Guide for Penetration Testers and Application Developers
Demystify the network behaviors of applications by leveraging the power of LD_PRELOAD! This blog post takes you on a journey to explore the inner workings of Linux applications as they communicate with the outside world.

Setting up a routed tunnel with SSH
Learn how to set up a secure SSH tunnel to pivot into a network during a pentest or CTF challenge with this step-by-step guide.

Cracking Werkzeug Debugger Console Pin
Learn how to crack the Werkzeug Debugger pin and gain access to the console in Python-based Flask web applications with this educational blog post.
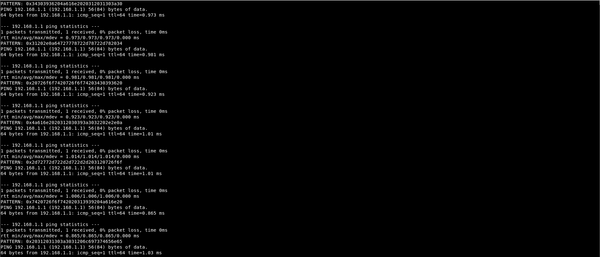
Slip(ping) out through the front door
A quick look at how we can exfiltrate data using the Linux ping command. This technique can transfer the output of Linux commands over the network to a target system using ICMP packets and the stock ping command.

Buffer Overflows and Exploit Development
So after making my video for my "Can You Hack It" series on the system Smasher from hack the box I realized that there is a lot of room to dig deeper and have more specialized tops related to the challenges from that system. So I decided that

Building a Better Rotten Pickle
An example of a simple scaffolding for creating python pickle payloads to abuse applications which allow control over input. This technique will allow you to write standard Python code for getting RCE and package it to auto-execute when loaded by the pickle module.

A Recipe For Rotten Pickles With Python
Part one in a two part series looking at how the python pickle language works and how it can be used to get remote code execution.